Hi.
I would like to exclude events that is showing up in the weird.log file that is OK. Here is an example of some events. Port 10050 is Zabbix and 3128 is a proxy server where it doesn’t like a connection to a googleapi service. My goal is to to eventually get the weird.log file to show only abnormal connections. How do I do this?
thanks,
Geoff
1673235644.435756 CsEAgs4WBj447UqTs5 192.168.120.7 59456 192.168.120.4 10050 data_before_established - F zeek TCP
1673235644.436273 CsEAgs4WBj447UqTs5 192.168.120.7 59456 192.168.120.4 10050 inappropriate_FIN - F zeek TCP
1673235648.790509 C7D38uZICjxSbsK9e 192.168.120.109 63989 192.168.120.4 3128 data_before_established - F zeek TCP
1673235648.832398 C7D38uZICjxSbsK9e 192.168.120.109 63989 192.168.120.4 3128 bad_HTTP_request - F zeek HTTP
1673235648.832398 C7D38uZICjxSbsK9e 192.168.120.109 63989 192.168.120.4 3128 line_terminated_with_single_CR - F zeek CONTENTLIN
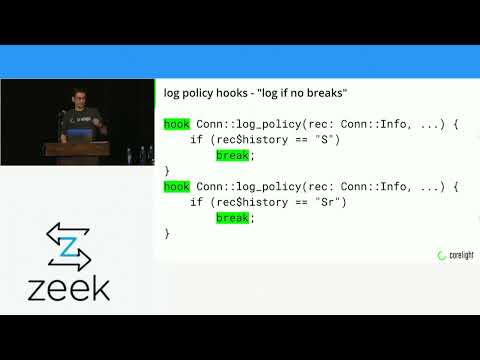
Justin’s ZeekWeek talk offers multiple ways to accomplish this, IIRC:
Thank you @Richard_Bejtlich, that looks promising.
I would like to exclude events that is showing up in the weird.log file that is OK.
As an aside, the weirds you point out aren’t necessarily “OK”. The data_before_established / inappropriate_FIN may indicate that Zeek was just started and missed part of the involved TCP connection, or packets are being dropped due to overload.
The bad_HTTP_request and line_terminated_with_single_CR may also be caused by dropped packets, or could indicate that client/server/proxy do not follow the protocol properly or Zeek’s HTTP parser not dealing properly with the traffic. If you see this regularly, it would be great if you could submit a pcap as a GitHub issue.
Great point Arne. OP, what does your capture loss log look like?
Richard
Hi Arne.
I see it continually, that is why I was trying to get rid of it in my logs through a whitelist.
Here is what it looks like in the different logs. I thought it was just the googleapi URL, but it appears to be a lot more hosts. I will get a capture of it and open up a github issue.
conn.log:1673278813.561882 CQixWk282I0KcVFto9 192.168.120.159 52826 192.168.120.4 3128 tcp - 0.343318 4047 0 S0 T T 0 ScADc 12 4539 00 -
dpd.log:1673278813.604738 CQixWk282I0KcVFto9 192.168.120.159 52826 192.168.120.4 3128 tcp HTTP not a http request line
http.log:1673278813.562333 CQixWk282I0KcVFto9 192.168.120.159 52826 192.168.120.4 3128 1 CONNECT wdcp.microsoft.com:443 wdcp.microsoft.com:443 - - - - 0 0- - - - (empty) - - - - - - - - -
weird.log:1673278813.562333 CQixWk282I0KcVFto9 192.168.120.159 52826 192.168.120.4 3128 data_before_established - F zeek TCP
weird.log:1673278813.604738 CQixWk282I0KcVFto9 192.168.120.159 52826 192.168.120.4 3128 bad_HTTP_request - F zeek HTTP
weird.log:1673278813.604738 CQixWk282I0KcVFto9 192.168.120.159 52826 192.168.120.4 3128 line_terminated_with_single_CR - F zeek CONTENTLINE
thanks,
Geoff
Actually, now that I am starting to see more traffic through this firewall (regular workday), the weird log is containing entries outside of the proxy.
root@fw1:/opt/zeek/spool/zeek# wc -l weird.log conn.log
1250 weird.log
1179 conn.log
So this is a completely different issue than the whitelist that I was originally looking for. I was only seeing the google api connection yesterday, which I could have dealt with through a filter.
Should I open another thread, since this one has been answered?
BTW, I am running version 5.1.1 on Ubuntu 22.04.
thanks,
Geoff
The conn.log history entry you shows indicates there are checksum errors: ScADc. Probably that’s what’s happening on your end. Searching for checksum errors and Zeek and the sniffing setup you use hopefully lets you find something. That one came up recently on GitHub 2673.
But yeah, makes sense to open a new thread for that if you’re stuck.